An Exploratory study into the aetiology of cybercrime:
Comparing the utility of the Routine Activities Theory using a model-comparison approach
Keywords:
routine activities theory, cybercrime, cyber-dependent, cyber-enabled, model comparison, human-centricAbstract
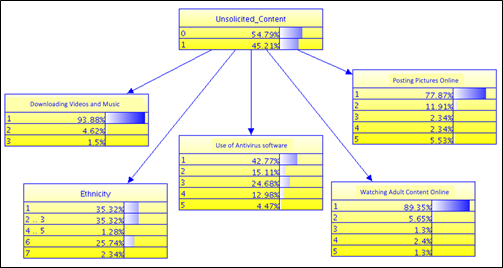
The study took a human-centric approach to exploring cybercrime victimization by comparing the utility of the Routine Activities Theory (RAT) between cyber-dependent (hacking and malware infection) and cyber-enabled (online harassment and unsolicited content) crime victimization. Data collection was done using a self-administered survey disseminated using chain referral sampling. The collected data was analyzed using Naïve Bayes, a supervised machine learning algorithm to develop classification and dependency models with B-Course v 2.0.0. This research found that the RAT showed greater utility with cyber-dependent crimes than cyber-enabled crimes, given the caveat that this outcome is based on the operationalization of the tenets of the RAT used in this study. Voluntary and involuntary personal information disclosure through social networking sites increased the likelihood of being a target of hacking, online harassment, and unsolicited content. Deviant online activities such as peer-to-peer downloads and watching pornography increase the risk of cyber-dependent crime victimization. Personal guardianship measures such as knowledge of cybercrime victimization and setting accounts to private (limiting uncontrolled access to personal information) are associated with cyber-dependent crimes. The study concluded that there is a difference in etiology between cyber-dependent and cyber-enabled crime in relation to victimization suggesting that all cybercrimes cannot be explained equally with general theories, which necessitates a typological approach to the study of cybercrime victimization.